Windows File Explorer has a separate panel that displays a list of favorite folders and locations called Quick Access. Many users and administrators unjustly ignore this handy Windows tool for quickly accessing your favorite folders. This article describes how to use PowerShell and Group Policies to automate the configuration of the Quick Access pane and pinned folders on Windows.
By default, the Quick Access panel displays only the standard user profile libraries (Desktop, Downloads, Pictures, Documents). Windows automatically adds folders the user has opened frequently (or recently) to Quick Access. The user can also manually pin any folder to the Quick Access pane. To do this, select the required folder on your computer or a shared folder on a remote computer and select the Pin to Quick Access option. A pushpin icon will appear next to the folder name in this case.
If your Windows doesn’t display the Quick Access pane, go to the HKLMSOFTWAREMicrosoftWindowsCurrentVersionExplorer registry key and delete the HubMode registry parameter with a value of 1 (File Explorer hides the Quick Access panel when this option is set). Previously, we showed how to hide the library and special folders in Windows File Explorer.
In my case, I want to pin certain folders to Quick Access, depending on the access groups (roles) that are assigned to the users. For example, accountants need one list of favorite folders, sales managers need another, and so on. Group Policy doesn’t have the built-in tools to centrally manage Quick Access, so PowerShell had to be used.
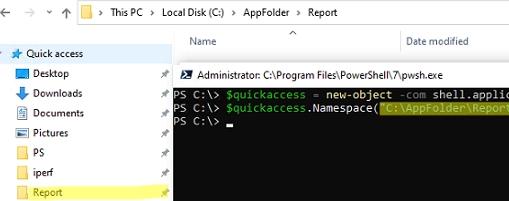
To add (pin) a specific folder to the Quick Access List, specify the path to the folder in the command:
$quickaccess = new-object -com shell.application
$quickaccess.Namespace(“C:CorpAppReport”).Self.InvokeVerb(“pintohome”)
%AppData%MicrosoftWindowsRecentAutomaticDestinationsf01b4d95cf55d32a.automaticDestinations-ms file. To quickly clear the Quick Access list, delete this file by running the command:del /f /s /q /a "%AppData%MicrosoftWindowsRecentAutomaticDestinationsf01b4d95cf55d32a.automaticDestinations-ms"
A local folder or a shared network folder (by UNC path) can be added to the Quick Access:
$quickaccess.Namespace("\munfs01publicsales").Self.InvokeVerb("pintohome")
Any user profile folder can be pinned
$quickaccess.Namespace("C:Users$($env:USERNAME)AppDataRoamingMyApp").Self.InvokeVerb("pintohome")
Remove (unpin) a folder from Quick Access:
($QuickAccess.Namespace("shell:::{679f85cb-0220-4080-b29b-5540cc05aab6}").Items() | where {$_.Path -eq "C:CorpAppReport"}).InvokeVerb("unpinfromhome")
You can remove any of the profile library folders that are pinned to Quick Access by default:
$quickaccess = new-object -com shell.application
$results=$QuickAccess.Namespace("shell:::{679f85cb-0220-4080-b29b-5540cc05aab6}").Items()
$DeleteDefaultItems = @("Desktop","Documents","Pictures","Videos","Downloads")
($results| where {$_.name -in $DeleteDefaultItems}).InvokeVerb("unpinfromhome")
Remove all pinned items from Quick Access:
($quickaccess.Namespace("shell:::{679f85cb-0220-4080-b29b-5540cc05aab6}").Items() | where { $_.IsFolder -eq "True"}).InvokeVerb("unpinfromhome")
The following PowerShell script adds folders to the Quick Access pane only if the user is a member of a specific AD group:
$usergroups=(New-Object System.DirectoryServices.DirectorySearcher("(&(objectCategory=User)(samAccountName=$($env:username)))")).FindOne().GetDirectoryEntry().memberOf
if ($usergroups.Contains(‘CN=MUN_SaleManagers,OU=Groups,OU=MUN,DC=woshub,DC=loc’))
{
$AddItems = @(
[pscustomobject]@{Name=Report;Path=”\woshub.locDFSReports”}
[pscustomobject]@{Name=’Scans’;Path=”\woshub.locDFSScans”}
[pscustomobject]@{Name=’Test1′;Path=”$env:USERPROFILEDownloads”}
)
ForEach ($Item in $AddItems)
{
if (($Item.Name -notin $results.Name) -and (Test-Path -Path $Item.path)) {
$QuickAccess.Namespace($Item.path).Self.InvokeVerb(“pintohome”)
}
}
}
If the user is a member of the MUN_SaleManagers group, this PowerShell script will check if the user’s QuickAccess list contains pinned folders from the $AddItems array. If such a folder is missing from the Quick Access, the script will check the availability of the specified path and pin the folder.
“`html
You can add several conditions to the script to check if the user is a member of other AD security groups. As a result, the PowerShell script will pin folders to the user’s Quick Access list based on their AD group membership.
Save this PowerShell to the \woshub.locNETLOGON folder on the AD domain controller (this allows ignoring PowerShell execution policy settings.) and run it as a user logon script using Group Policy (more information about running PowerShell scripts via GPO).
“`